Security
Everything we do begins with security.
Trust
Surgical Notes focuses on applying administrative, physical, and technical measures to safeguard our data. This reduces outsourcing risks and fosters trust with our partners. We collaborate closely with our clients and their suppliers by participating in comprehensive security reviews, providing compliance documentation, and entering into legally binding agreements. As regulatory requirements evolve, we continuously adapt.
Performance
Our applications and systems automatically scale to meet the availability and performance demands placed on it by our clients and users. We also monitor and measure application performance within our technical architecture which is built upon a hybrid cloud environment leveraging Microsoft Azure capabilities such as serverless computing, cognitive services, and analytics.
Business Continuity
Surgical Notes’ disaster recovery and business continuity initiatives ensure that clients have consistent access to our technology and services. We use collocated data centers and Microsoft Azure Site Recovery to minimize service interruptions. Our application resiliency and availability are supported by a 99.99% uptime, excluding scheduled downtimes for maintenance activities.
We take our responsibility seriously to protect the data you entrust to us.
Client Privacy Rights
Surgical Notes will only use client data to carry out the work contracted by our clients. We demonstrate complete transparency processing the data in our care. Our clients have the following privacy rights:
- Identify who has had access to your data, when, where, how, and what is done with it
- Request correction to, limitation of, or destruction of your data in a compliant fashion
- Withdraw consent to our handling of your data
- Opt-out of marketing communications
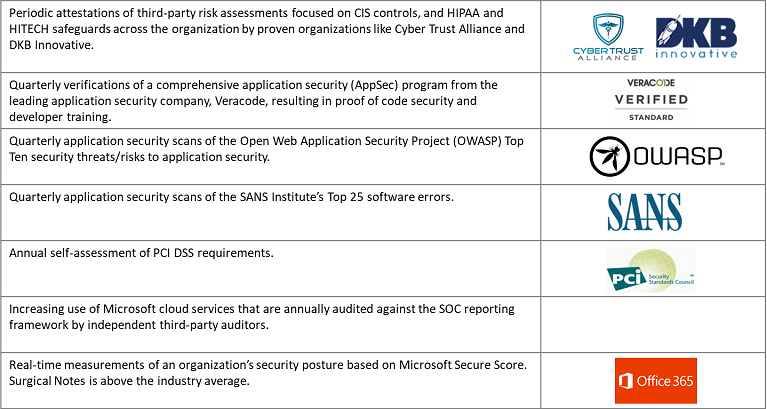
Information Technology Security & Compliance
Surgical Notes and its partners’ technologies and services comply with various security best practices and standard-setting bodies, as applicable. In addition to our security program, our rigorous compliance measures demonstrate our commitment to protecting our clients and client data.